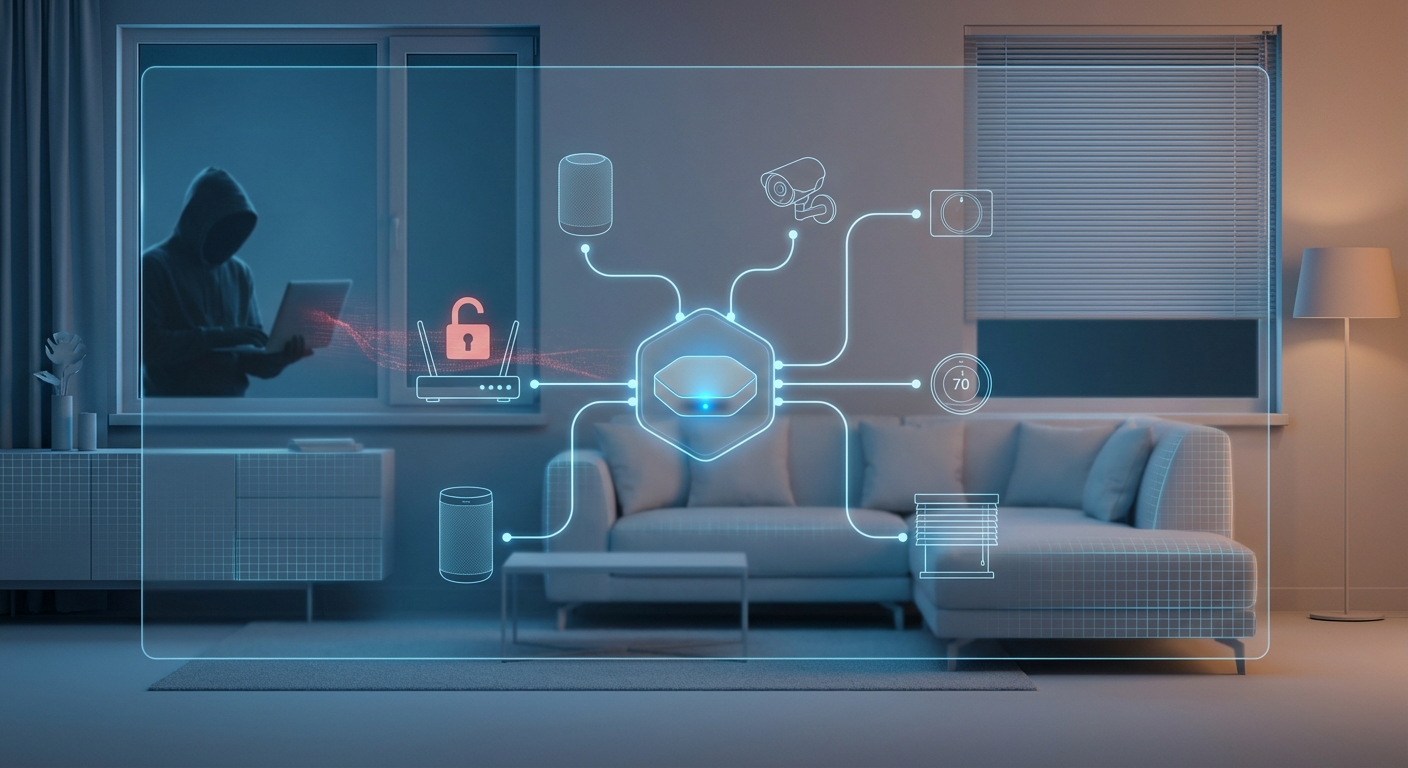
Your smart doorbell just rang. You check the app and see a delivery driver at your door. Convenient, right? But what if someone else is watching that same feed? What if they can unlock your door remotely? Smart home devices promise comfort and control, but they also create new vulnerabilities that most homeowners never consider until it’s too late.
Smart home devices face serious security threats including weak default passwords, unencrypted data transmission, outdated firmware, and vulnerable network configurations. Hackers can exploit these weaknesses to access cameras, unlock doors, steal personal data, or launch larger attacks. Protecting your connected home requires strong passwords, network segmentation, regular updates, and understanding which devices pose the greatest risk to your privacy and safety.
The hidden vulnerabilities in your connected home
Most people set up their smart devices and forget about them. The thermostat adjusts itself. The lights turn on at sunset. Everything works smoothly until it doesn’t.
The problem is that each connected device is a potential entry point. Your smart refrigerator might seem harmless, but it connects to the same network as your laptop and phone. If a hacker compromises that refrigerator, they can potentially access everything else on your network.
Many devices ship with default passwords like “admin” or “12345.” Manufacturers expect users to change these immediately. Most never do. Security researchers have found thousands of devices still using factory settings, creating an open invitation for anyone with basic hacking knowledge.
Data transmission is another weak spot. Some devices send information without encryption. That means anyone monitoring your network traffic can see what you’re doing. They might intercept video feeds from your security camera or listen to conversations picked up by your smart speaker.
Devices that pose the biggest threats

Not all smart home gadgets carry the same level of risk. Some handle sensitive data or control physical access to your home. Others collect information about your daily routines.
Security cameras top the list of vulnerable devices. When compromised, they give strangers a window into your private life. Hackers have accessed baby monitors, bedroom cameras, and outdoor security systems. Some have even spoken to children through compromised devices.
Smart locks present a different danger. If someone gains access to your lock’s control system, they can unlock your door remotely. They might wait until you leave for vacation, then enter your home without breaking anything. No forced entry means delayed detection.
Voice assistants like smart speakers constantly listen for wake words. While companies claim they only record after activation, vulnerabilities have allowed unauthorized recording. These devices also store conversation history, purchase records, and personal preferences that hackers find valuable.
Here’s a breakdown of common devices and their primary vulnerabilities:
| Device Type | Main Security Risk | Potential Impact |
|---|---|---|
| Security Cameras | Weak passwords, exposed feeds | Privacy invasion, surveillance |
| Smart Locks | Cloud service breaches | Unauthorized physical access |
| Voice Assistants | Always-on microphones | Eavesdropping, data theft |
| Smart Thermostats | Network access points | Gateway to other devices |
| Smart TVs | Built-in cameras, data collection | Spying, tracking habits |
| Video Doorbells | Unencrypted streams | Monitoring routines, planning break-ins |
Smart thermostats might seem low risk, but they often have privileged network access. Hackers use them as stepping stones to reach more sensitive devices. The same applies to smart plugs, light bulbs, and other seemingly innocent gadgets.
How attackers exploit your smart home
Understanding attack methods helps you defend against them. Hackers don’t need sophisticated tools to compromise most smart homes. They use predictable patterns and common mistakes.
The first step is usually network scanning. Attackers identify connected devices by looking for specific signatures. They check which ports are open and what services are running. This reconnaissance reveals which devices are present and potentially vulnerable.
Once they identify targets, they attempt default credentials. Automated tools try common username and password combinations across thousands of devices simultaneously. Success rates are surprisingly high because so few people change factory settings.
Firmware exploits come next. Older devices often have known vulnerabilities that manufacturers never patched. Hackers maintain databases of these flaws and target devices that haven’t been updated. Some devices never receive updates at all, remaining permanently vulnerable.
Man-in-the-middle attacks intercept communication between devices and their cloud services. Without proper encryption, attackers can read, modify, or inject commands. They might send fake instructions to your smart lock or alter temperature settings on your thermostat.
“The weakest link in smart home security isn’t the technology itself, but the human assumption that convenience and security can coexist without effort. Every connected device requires active management, not passive trust.” – Cybersecurity researcher
Real consequences of compromised devices

The impact of smart home breaches goes beyond theoretical risk. Real families have experienced serious consequences.
One family discovered their security camera had been hacked when a stranger’s voice came through the speaker, taunting their young daughter. The hacker had been watching for days, learning their routines before revealing himself.
Another homeowner returned from vacation to find their house ransacked. The thieves had accessed their smart doorbell, monitoring when packages arrived and when the family left. They knew exactly when the house would be empty.
Privacy violations can be subtle but damaging. Hackers have sold access to compromised camera feeds on dark web forums. Strangers pay to watch people in their homes, completely unaware they’re being observed.
Financial theft occurs when attackers access devices linked to payment methods. Smart speakers with purchasing capabilities, connected door locks with service subscriptions, and other devices store payment information that can be exploited.
Identity theft becomes easier with smart home data. Attackers gather information about your schedule, habits, family members, and preferences. They use this to craft convincing phishing attempts or answer security questions for other accounts.
Steps to secure your connected ecosystem
Protecting your smart home requires systematic action. Follow these steps to significantly reduce your risk:
-
Change every default password immediately after setup. Use unique, strong passwords for each device. Password managers make this manageable.
-
Create a separate network for smart home devices. Most routers support guest networks. Put your IoT devices there, isolated from computers and phones that contain sensitive data.
-
Enable two-factor authentication wherever available. This adds a critical layer of protection even if passwords are compromised.
-
Update firmware regularly. Check for updates monthly, or enable automatic updates if the manufacturer offers them reliably.
-
Disable features you don’t use. Remote access, voice purchasing, and always-on microphones create unnecessary risks if you don’t need them.
-
Research devices before purchasing. Look for manufacturers with strong security track records and commitment to ongoing updates.
-
Monitor your network for unusual activity. Many routers offer traffic monitoring that can alert you to suspicious behavior.
Common mistakes that leave you exposed

Even security-conscious homeowners make critical errors. Avoid these common pitfalls:
- Using the same password across multiple devices creates a domino effect when one is compromised
- Ignoring update notifications because they seem inconvenient
- Connecting devices to public WiFi networks that lack proper security
- Sharing device access with too many people or not revoking access when relationships change
- Assuming expensive devices have better security than budget options
- Trusting that manufacturers will maintain security without verification
- Placing cameras in sensitive areas like bedrooms or bathrooms
- Failing to change passwords after service technicians or previous homeowners had access
The “set it and forget it” mentality is particularly dangerous. Smart home security requires ongoing attention. Threats evolve, new vulnerabilities emerge, and manufacturers sometimes abandon older products.
Privacy concerns beyond hacking
Security breaches aren’t the only privacy issue. Many devices collect far more data than necessary for their function. Manufacturers use this information for advertising, product development, or sell it to third parties.
Smart TVs track viewing habits in detail. They know what you watch, when you watch it, and how long you pay attention. This data builds detailed profiles used for targeted advertising.
Voice assistants record conversations, sometimes when not activated. While companies claim these recordings improve accuracy, they also employ human reviewers who listen to clips. Your private conversations might be heard by strangers.
Location tracking through smart home devices reveals when you’re home or away. This information has value for marketers, insurance companies, and others. Data breaches can expose this sensitive information to anyone.
Read privacy policies before connecting devices. Understand what data is collected, how it’s used, and whether you can opt out. Many devices offer privacy settings that aren’t enabled by default.
Building a security-first smart home

Creating a secure connected home doesn’t mean abandoning convenience. It means making informed choices and maintaining good habits.
Start small. Don’t connect everything at once. Add devices gradually, securing each one properly before adding the next. This measured approach makes security management more sustainable.
Prioritize devices by risk level. Secure cameras, locks, and other high-risk devices first. Less critical devices like smart bulbs can wait.
Choose manufacturers carefully. Look for companies that:
- Provide regular security updates
- Have transparent privacy policies
- Offer strong encryption by default
- Support security features like two-factor authentication
- Have responsive customer security teams
- Don’t require cloud connectivity for basic functions
Consider local control options. Devices that work without cloud services reduce your attack surface. They’re harder to access remotely, which protects against many common attacks.
Document your setup. Keep a list of all connected devices, their passwords, and last update dates. This inventory helps you maintain security over time and identify devices that need attention.
When to disconnect devices
Sometimes the best security decision is removing a device entirely. Consider disconnecting when:
The manufacturer stops providing security updates. Unsupported devices become increasingly vulnerable over time. No amount of password strength compensates for unpatched vulnerabilities.
A device has been compromised. Even after cleaning malware, residual access might remain. Replacing compromised devices provides peace of mind.
You discover the manufacturer has poor security practices. If a company suffers repeated breaches or ignores reported vulnerabilities, their products don’t belong in your home.
The device collects more data than you’re comfortable sharing. Privacy preferences change. A device that seemed acceptable initially might cross your boundaries later.
You simply don’t use it anymore. Unused devices still create risk. If that smart coffee maker sits unplugged, remove it from your network entirely.
Staying ahead of emerging threats
Smart home security isn’t static. New threats appear constantly, and yesterday’s best practices might not protect you tomorrow.
Follow security news related to your specific devices. Subscribe to manufacturer security bulletins. Join online communities where users share vulnerability discoveries and protective measures.
Audit your setup quarterly. Review connected devices, check for available updates, and verify security settings haven’t changed. Firmware updates sometimes reset configurations to defaults.
Test your security periodically. Try accessing your devices from outside your network. Verify that protections work as intended. Consider hiring professionals for annual security assessments if you have many connected devices.
Stay informed about new attack methods. Hackers constantly develop new techniques. Understanding current threats helps you prioritize protective measures.
Making security sustainable
The biggest challenge isn’t implementing security measures once. It’s maintaining them over months and years.
Create a routine. Schedule monthly security checks like you would other home maintenance. Spend 30 minutes reviewing devices, checking for updates, and verifying settings.
Automate what you can. Enable automatic updates where reliable. Set calendar reminders for tasks that can’t be automated.
Make it manageable. Don’t let perfect become the enemy of good. Basic security consistently applied beats comprehensive measures that you abandon after a few weeks.
Involve your household. Everyone who uses smart devices should understand basic security practices. Family members need to know not to share passwords or click suspicious links.
Your connected home, your responsibility
Smart home technology will only become more prevalent. More devices, deeper integration, greater convenience. But also expanded attack surfaces and new vulnerabilities.
Manufacturers will improve security over time, but they can’t protect you from weak passwords or ignored updates. The responsibility ultimately falls on you as the homeowner.
Start today. Pick one device and secure it properly. Change the password, check for updates, review privacy settings. Then move to the next one. Small, consistent actions build robust protection over time.
Your smart home should work for you, not expose you. With proper security practices, you can enjoy the convenience of connected devices without sacrificing your privacy or safety. The choice is yours, but make it an informed one.