You just received an email. A company you trust has been breached. Your name, email, maybe even your credit card details are now in the hands of strangers. The notification is vague, the apology generic. But what actually happens next? Where does your data go, and what do criminals do with it?
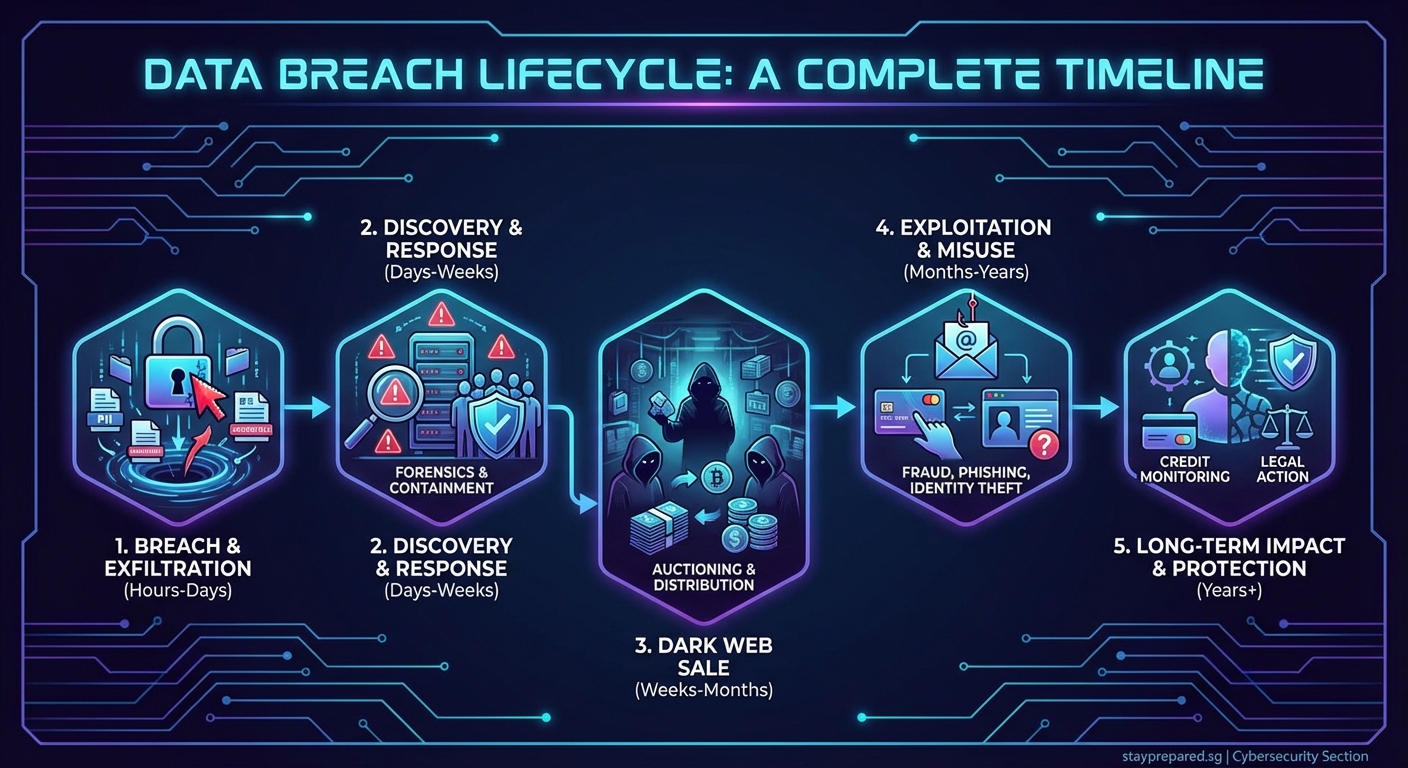
After a data breach, your information follows a predictable path: discovery, extraction, sale on dark web marketplaces, and exploitation through fraud or identity theft. Companies must notify affected users, investigate the incident, and offer remediation services. Meanwhile, criminals work fast to monetize stolen data before security measures catch up. Understanding this timeline helps you respond effectively and protect yourself from long-term damage.
The first 24 hours: detection and panic
Most breaches aren’t discovered immediately. On average, companies take 207 days to identify a security incident. But once they do, the clock starts ticking.
Internal security teams or external researchers notice unusual activity. Database queries that shouldn’t exist. Files moving to unknown servers. Login attempts from suspicious locations. The breach might have started months ago, but this is when the company knows something is wrong.
Leadership gets pulled into emergency meetings. Legal teams assess liability. PR departments draft statements. Everyone wants to know the same things: how bad is it, what was taken, and who can we blame?
During this chaos, your data is already moving. Attackers extract files as fast as possible before access gets cut off. They compress databases, hide their tracks, and prepare for the next phase.
What attackers do with your stolen data
Once criminals have your information, they sort it by value. Not all data is equal.
Credit card numbers with CVV codes sell for $5 to $50 each, depending on the card limit and country. Full identity packages including name, address, Social Security number, and date of birth go for $8 to $50. Medical records fetch even more, sometimes $250 per file, because they contain insurance details and can’t be changed like a credit card.
Email addresses and passwords end up in credential stuffing attacks. Bots try your leaked password on thousands of other sites, hoping you reused it. If you used the same login for your bank, streaming service, and shopping accounts, all of them are now vulnerable.
Personal details get bundled and sold on dark web marketplaces. These sites look surprisingly normal, with product listings, customer reviews, and even refund policies. Buyers include other criminals, identity thieves, and sometimes competitors looking for corporate intelligence.
Here’s what different types of stolen data typically enable:
| Data Type | Common Use | Time to Exploit |
|---|---|---|
| Credit card numbers | Fraudulent purchases | Hours to days |
| Login credentials | Account takeover | Immediate |
| Social Security numbers | Identity theft, tax fraud | Weeks to months |
| Medical records | Insurance fraud | Months to years |
| Personal emails | Phishing campaigns | Days to weeks |
| Corporate documents | Espionage, extortion | Varies widely |
The company’s response timeline
While criminals work fast, companies move through a structured response process. This isn’t just internal policy. Laws like GDPR and state breach notification requirements force specific actions.
Days 1 to 3: containment
Security teams isolate affected systems. They patch vulnerabilities, reset credentials, and try to stop ongoing data exfiltration. This is digital triage. Stop the bleeding first, assess damage later.
Days 4 to 10: investigation
Forensic experts trace the attack. How did intruders get in? What did they access? How long were they inside? This investigation determines what gets disclosed and to whom.
Days 11 to 30: notification
Companies must notify affected individuals, usually within 30 to 60 days depending on jurisdiction. These emails are often maddeningly vague because legal teams limit what can be said during ongoing investigations.
You’ll see phrases like “we take your privacy seriously” and “out of an abundance of caution.” Translation: we’re legally required to tell you, but we don’t want to admit how bad this is.
Months 2 to 6: remediation
Companies offer credit monitoring services, usually for one to two years. They implement new security measures. They face lawsuits. They testify before regulators.
But here’s the truth: by month two, most companies have moved on. Your data is still out there, but the breach is old news.
What happens to your information long term

Stolen data doesn’t expire. It circulates for years.
Criminals use it in waves. The first wave hits immediately, with fraudulent charges and account takeovers. The second wave comes months later, after you’ve relaxed and stopped monitoring your accounts so closely. The third wave can hit years down the line, when someone uses your old information to open new accounts or file fake tax returns.
Your email address ends up on spam lists forever. Phishing attempts increase because attackers know which company you do business with. They craft convincing fake emails that reference the breach, claiming you need to “verify your account” or “update your security settings.”
“The biggest mistake people make after a breach is assuming the danger passes once they change their password. Your personal information can’t be changed like a password. Once it’s out there, you need permanent vigilance, not temporary fixes.” — Security researcher
Social Security numbers and birthdates never change. If those leaked, you face lifetime risk. Someone could use your identity to open credit cards, take out loans, or commit crimes in your name years after the original breach.
Steps you should take immediately
When you learn about a breach affecting your data, follow this sequence:
- Change your password for the breached service using a strong, unique combination you’ve never used before.
- Enable two-factor authentication on the affected account and any other important accounts.
- Check your other accounts for suspicious activity, especially if you reused that password anywhere else.
- Place a fraud alert with credit bureaus, which makes it harder for someone to open new accounts in your name.
- Review your credit reports from all three bureaus for accounts you didn’t open.
- Monitor your financial statements closely for at least six months, checking for small test charges criminals use to verify stolen cards.
- Consider a credit freeze if sensitive information like your Social Security number was compromised.
Don’t wait for the company to offer credit monitoring. Set up your own alerts. Most banks and credit cards offer free transaction notifications. Use them.
The regulatory aftermath
Breached companies face consequences beyond angry customers. Regulators investigate whether the company followed security best practices and notification laws.
The EU’s GDPR allows fines up to 4% of global annual revenue. California’s CCPA enables penalties of $7,500 per violation. These aren’t small numbers. A breach affecting one million people could theoretically result in $7.5 billion in fines under CCPA.
In practice, penalties are lower but still significant. British Airways paid £20 million for a 2018 breach. Marriott paid £18.4 million for exposing 339 million guest records. Equifax settled for up to $700 million after exposing 147 million people.
These penalties incentivize better security. But they don’t undo the damage to individuals whose data was stolen.
Why some breaches hurt more than others
Not every breach creates equal risk. Context matters.
A breach of your email address from a newsletter signup is annoying. A breach of your full identity from a credit bureau is catastrophic. The difference lies in what was taken and what it enables.
Ask these questions when you hear about a breach:
- What specific data was compromised?
- Was it encrypted or stored in plain text?
- Did it include passwords, and were they properly hashed?
- How long did attackers have access?
- What can someone do with this specific combination of data?
A breach that exposes only email addresses is manageable. A breach that exposes email, password, security questions, and partial Social Security numbers is a crisis. The company’s notification should specify what was taken, but many stay vague to limit liability.
The dark web marketplace economy
Your data enters an underground economy with its own rules and market dynamics. Prices fluctuate based on supply and demand.
After a major breach, prices drop because supply floods the market. Fresh credit cards that sold for $30 before a breach might drop to $5 after millions hit the market. Buyers know companies will cancel and reissue cards quickly, reducing the window for fraud.
But less common data holds value longer. If a small healthcare provider gets breached, those medical records might command premium prices because they’re rare and detailed.
Marketplaces operate like legitimate businesses. Sellers build reputations. Buyers leave reviews. Escrow services prevent scams. Some marketplaces even offer customer support if your purchased data “doesn’t work.”
This professionalization makes the problem worse. Lower barriers to entry mean more criminals can participate. You don’t need technical skills to buy stolen data and commit fraud anymore.
When companies don’t tell you
Not every breach becomes public. Companies sometimes discover breaches but can’t determine what was accessed. Others find breaches that exposed systems but maybe not data. Some simply hope no one notices.
This is why you should assume your information has been compromised somewhere, even if you’ve never received a notification. With billions of records stolen each year, the odds are against you.
Proactive monitoring matters more than waiting for notifications. Services that scan for your email address in known breaches can alert you before companies do. Many password managers include this feature.
Living in a post-breach world
The uncomfortable truth is that data breaches are now routine. Your information has probably been stolen multiple times from different companies. The question isn’t if you’ll be affected, but how you’ll respond.
This doesn’t mean giving up. It means adjusting your security posture to match reality. Use unique passwords for every account. Enable two-factor authentication everywhere possible. Monitor your credit regularly. Treat your personal information as already compromised and plan accordingly.
Companies will keep getting breached. Criminals will keep selling data. But you can make yourself a harder target by understanding what happens after a breach and responding faster than most people do.
The timeline from breach to fraud is measured in hours and days, not weeks or months. Your response needs to match that speed. The company that lost your data will eventually move on. You can’t afford to.
