You just found out your company’s data has been compromised. Your heart is racing, your inbox is filling up, and you’re not sure where to start.
The first few hours after discovering a breach will determine how much damage your organization suffers. Every minute counts, and panic is your worst enemy right now.
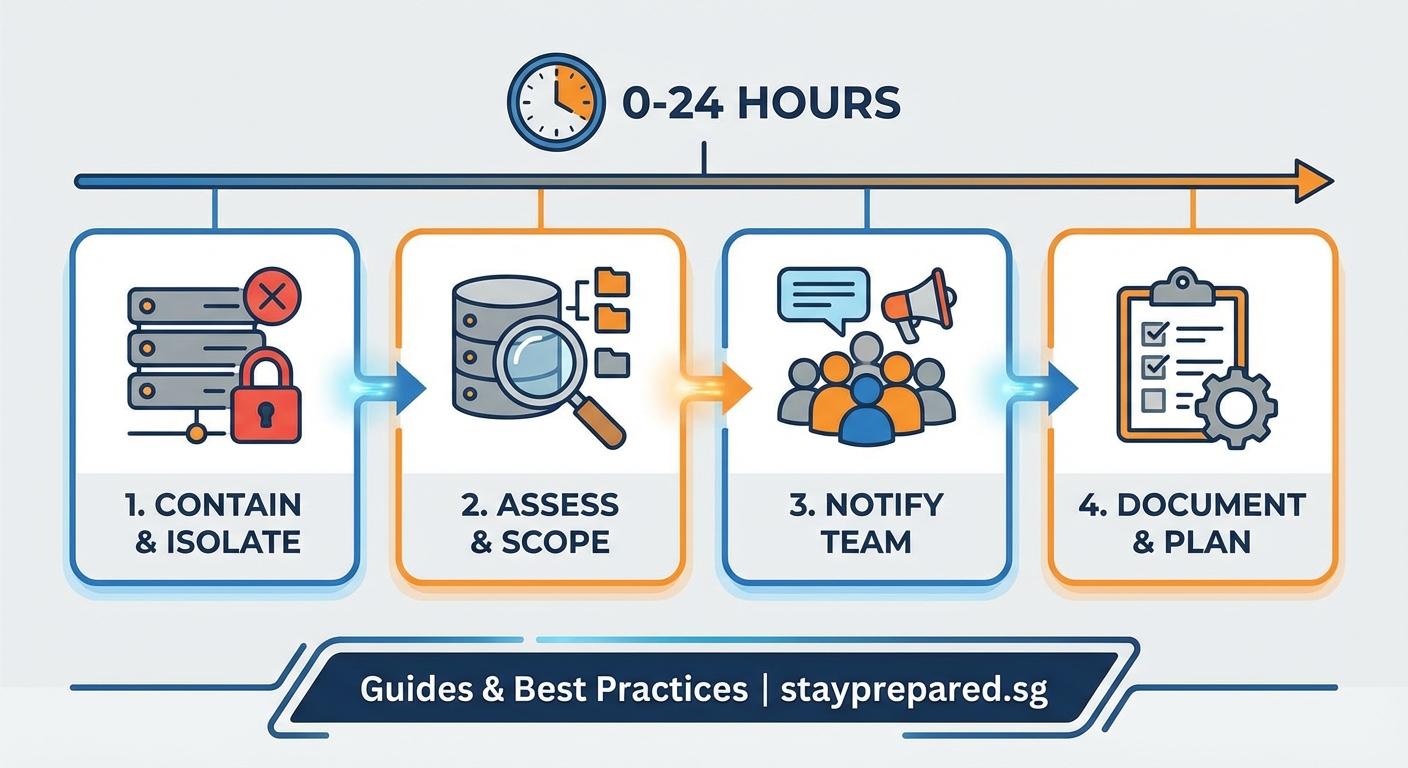
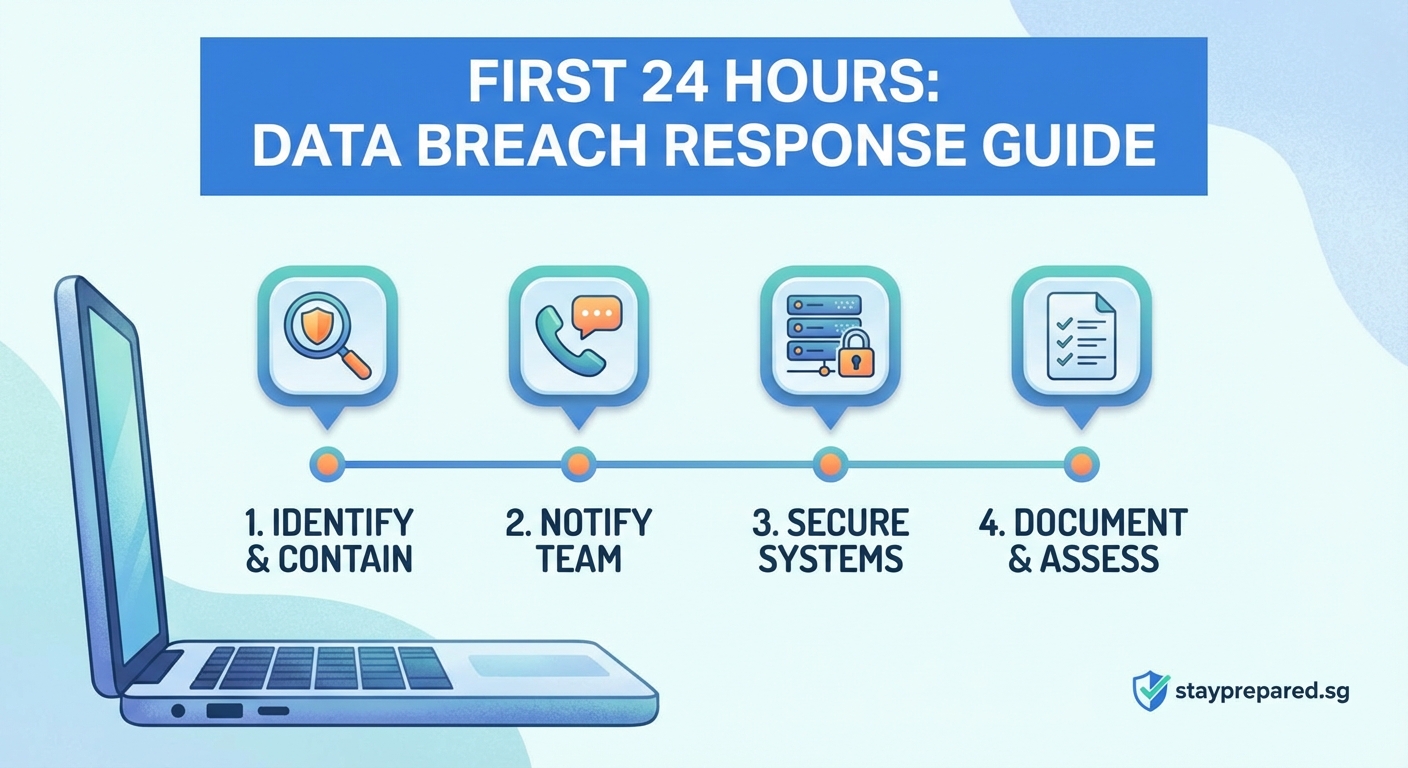
After discovering a data breach, immediately activate your incident response team, contain the threat by isolating affected systems, preserve all evidence, assess the scope of compromised data, notify relevant authorities within required timeframes, communicate transparently with affected parties, and document every action taken. Speed and methodical execution during these first hours will minimize damage and protect your organization’s reputation.
Stop the bleeding first
Your initial priority is containment. Think of a data breach like a fire: you need to stop it from spreading before you worry about cleanup.
Isolate compromised systems from your network immediately. This might mean physically disconnecting servers, disabling network access, or shutting down specific services. Yes, this will disrupt operations. But continued exposure will cause far greater harm.
Don’t delete anything yet. Resist the urge to wipe systems clean or remove suspicious files. You need that evidence for investigation, legal proceedings, and regulatory compliance. Preservation comes before cleanup.
Change credentials for all administrative accounts, especially those that might have been exposed. Attackers often establish multiple backdoors, so closing one entry point isn’t enough.
Assemble your response team
You can’t handle this alone, and you shouldn’t try.
Your incident response team should include:
- IT security personnel who understand your infrastructure
- Legal counsel familiar with data protection laws
- Communications professionals who can handle internal and external messaging
- Senior leadership with decision making authority
- Human resources if employee data is involved
- External forensics experts for complex investigations
Get everyone on a secure communication channel. Don’t use potentially compromised email systems. Consider using encrypted messaging apps or a separate incident response platform.
Assign clear roles immediately. Who documents actions? Who communicates with stakeholders? Who handles technical containment? Confusion wastes precious time.
Figure out what happened
You need to understand the scope before you can respond appropriately.
Start by identifying which systems were accessed. Review access logs, security alerts, and any indicators of compromise. Look for unusual login times, unfamiliar IP addresses, or abnormal data transfers.
Determine what data was exposed. Customer information? Financial records? Health data? Intellectual property? The type of data affected will determine your legal obligations and communication strategy.
Establish a timeline. When did the breach start? How long did attackers have access? Was this a targeted attack or opportunistic? Understanding the sequence helps you assess damage and prevent future incidents.
| Investigation Focus | What to Look For | Why It Matters |
|---|---|---|
| Entry point | Phishing emails, unpatched vulnerabilities, stolen credentials | Prevents repeat attacks through the same vector |
| Data accessed | File access logs, database queries, exfiltration patterns | Determines notification requirements and legal exposure |
| Attacker behavior | Dwell time, lateral movement, persistence mechanisms | Reveals sophistication and potential ongoing threats |
| Business impact | Affected customers, operational disruption, financial exposure | Guides resource allocation and recovery priorities |
Don’t assume you’ve found everything on the first pass. Sophisticated attackers hide their tracks and establish multiple persistence mechanisms.
Know your legal obligations
Data breach notification laws vary by jurisdiction, industry, and data type. Ignorance won’t protect you from penalties.
Most regulations require notification within specific timeframes. The EU’s GDPR requires notification within 72 hours of discovery. Many US state laws have similar requirements. Some industry specific regulations have even tighter windows.
Contact your legal team immediately to determine your obligations. They’ll help you understand:
- Which regulators must be notified and when
- Whether law enforcement should be involved
- What affected individuals need to be told
- How to preserve attorney client privilege during investigation
- Potential liability exposure and insurance claims
Document everything with timestamps. Your actions during the response will be scrutinized later by regulators, customers, and possibly courts.
“The companies that survive breaches best are those that treat legal compliance as a floor, not a ceiling. Meeting minimum notification requirements isn’t enough. Transparency and proactive communication build trust that regulatory filings alone cannot.” – Cybersecurity incident response consultant
Communicate carefully but honestly
How you communicate about the breach will shape public perception and customer trust.
Start with internal communication. Employees need to know what happened, what’s being done, and how they should respond to questions. Give them specific talking points. Uncontrolled internal rumors can damage your response efforts.
Notify affected individuals as soon as you have accurate information. Waiting too long erodes trust. Sharing incomplete information causes confusion. Find the balance.
Your notification should include:
- What happened in clear, non technical language
- What specific information was compromised
- What you’re doing to address the situation
- What steps affected individuals should take to protect themselves
- How they can get more information or assistance
- Contact information for questions
Be honest about what you don’t know yet. Saying “we’re still investigating the full scope” is better than speculation or minimization.
Prepare for media inquiries. Designate a single spokesperson. Inconsistent messages from multiple sources create credibility problems.
Take care of affected people
Your customers, employees, or partners didn’t choose to have their data compromised. Your response should reflect that.
Offer credit monitoring services if financial information was exposed. This costs money but demonstrates accountability and helps prevent identity theft.
Set up a dedicated hotline or support channel for breach related questions. Train staff to handle these inquiries with empathy and accuracy.
Consider whether additional protective measures are appropriate. Password resets? Multi factor authentication requirements? Enhanced monitoring?
Don’t make affected people jump through hoops to get help. Complicated claim processes or unresponsive support teams compound the damage.
Document everything
Your documentation serves multiple purposes: regulatory compliance, insurance claims, legal defense, and future prevention.
Create a detailed timeline of events. Include:
- When the breach was discovered and by whom
- Initial assessment findings
- Containment actions taken with timestamps
- Team members involved and their roles
- Communications sent and to whom
- Evidence preserved and where it’s stored
- External parties engaged (forensics, legal, PR)
- Costs incurred for response activities
Keep contemporaneous notes. Don’t try to reconstruct the timeline days later from memory. Real time documentation is more accurate and more credible.
Preserve all evidence with proper chain of custody procedures. Compromised systems, log files, and communications may be needed for legal proceedings or regulatory investigations.
Common mistakes that make things worse
Even experienced teams make errors under pressure. Avoid these pitfalls.
| Mistake | Why It’s Harmful | Better Approach |
|---|---|---|
| Delaying notification to “investigate fully” | Violates legal requirements and destroys trust | Notify within required timeframes with available information |
| Minimizing the breach publicly | Creates credibility gap when full scope emerges | Be honest about uncertainty and committed to transparency |
| Failing to preserve evidence | Undermines investigation and legal defense | Isolate and protect compromised systems immediately |
| Using compromised systems for response | Alerts attackers and compromises communications | Establish separate, secure communication channels |
| Going it alone without experts | Misses sophisticated threats and legal nuances | Engage forensics and legal counsel early |
Don’t assume the breach is over just because you’ve closed one vulnerability. Conduct thorough forensics to identify all compromise indicators.
Plan for the long term
The immediate crisis will pass, but your work isn’t done.
Conduct a thorough post incident review once the acute response phase ends. What worked? What didn’t? How can you improve?
Implement lessons learned. Update your incident response plan. Address the vulnerabilities that allowed the breach. Improve monitoring and detection capabilities.
Consider whether organizational changes are needed. Do you need dedicated security staff? Better security training? Different vendor relationships?
Rebuild trust through action, not just words. Show customers and stakeholders that you’ve made meaningful improvements.
Monitor for ongoing threats. Breached credentials often circulate for months or years. Implement enhanced monitoring for affected accounts.
Your response defines your reputation
How you handle the hours and days after discovering a breach will be remembered long after the technical details are forgotten.
Organizations that respond with transparency, urgency, and genuine concern for affected people often emerge with their reputations intact or even enhanced. Those that minimize, delay, or deflect responsibility suffer lasting damage.
You didn’t choose to have a breach, but you can choose how to respond. Take action now, communicate honestly, and focus on protecting the people whose data you’re responsible for. That’s what separates organizations that survive crises from those that don’t.
