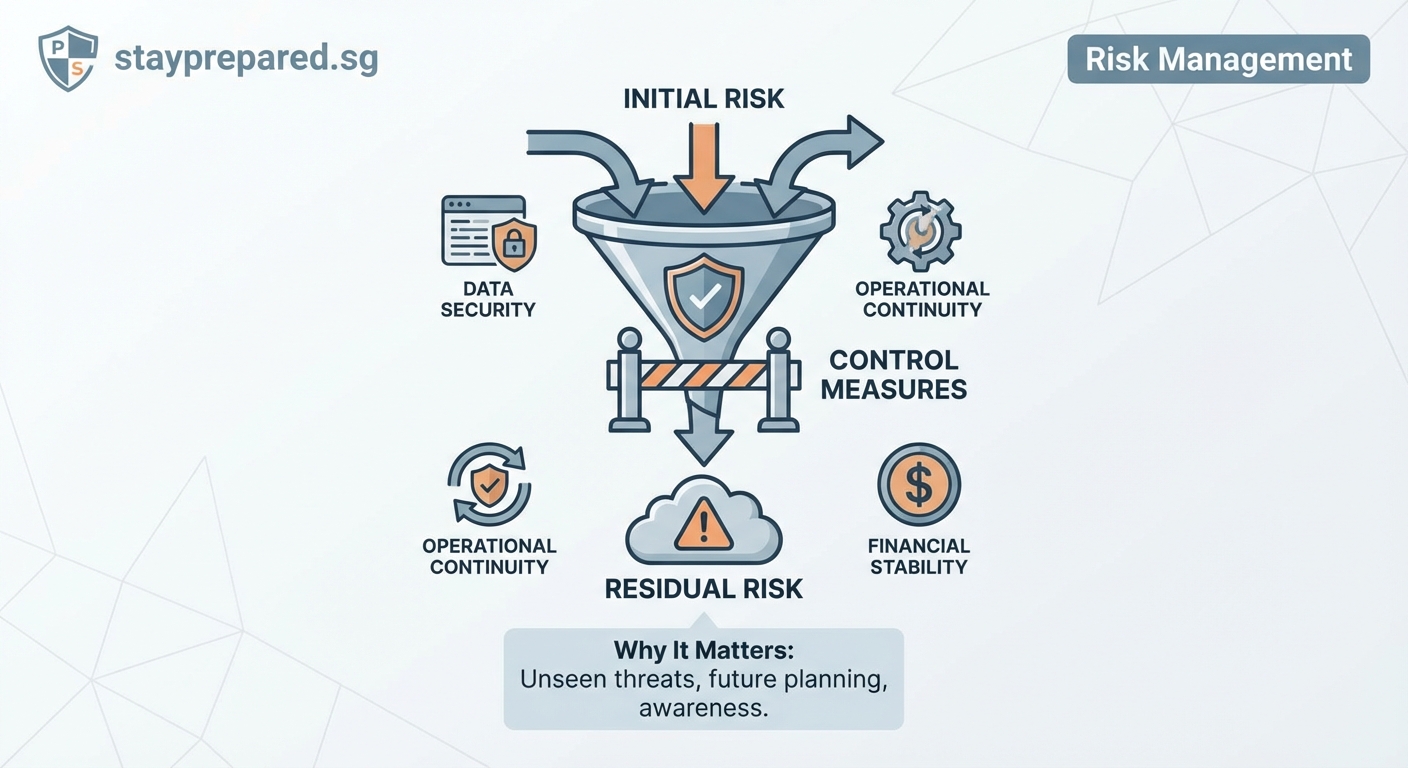
You implement security controls. You follow compliance frameworks. You train your team. But here’s the reality: risk never disappears completely. What stays behind after all your efforts is residual risk, and understanding it separates organizations that react from those that plan ahead.
Residual risk is the remaining exposure after implementing controls and mitigation strategies. It represents the gap between inherent risk and your organization’s risk tolerance. Managing residual risk requires continuous monitoring, informed acceptance decisions, and clear documentation to ensure threats stay within acceptable boundaries while supporting business objectives and compliance requirements.
Understanding residual risk in practical terms
Residual risk represents the threat level that persists after you’ve applied all reasonable security measures, controls, and mitigation strategies. Think of it as the unavoidable exposure that comes with doing business in an imperfect world.
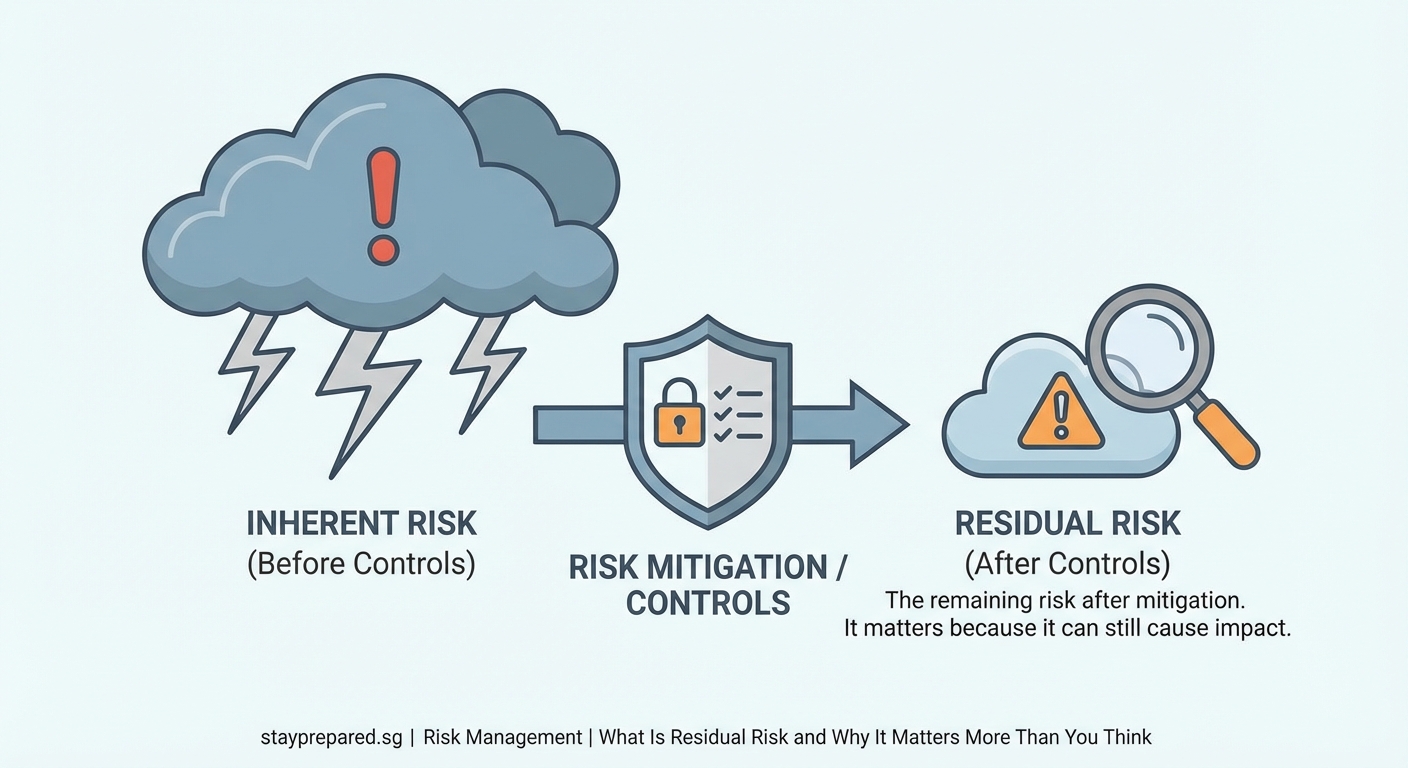
Every organization faces inherent risk. That’s the raw, uncontrolled threat level before any protective measures exist. When you add firewalls, encryption, access controls, or training programs, you reduce that inherent risk. What remains is residual risk.
Here’s a concrete example. A healthcare provider faces inherent risk from unauthorized access to patient records. They implement multi-factor authentication, role-based access controls, and encryption. These controls dramatically reduce the threat. But residual risk still exists because employees might fall for sophisticated phishing attacks, or a zero-day vulnerability could bypass current defenses.
The key difference between inherent and residual risk comes down to action. Inherent risk is theoretical. Residual risk is practical. It’s what you actually live with after spending budget, time, and effort on security.
Why residual risk matters for decision making
Risk management isn’t about eliminating all threats. That’s impossible and economically unfeasible. Instead, it’s about making informed choices about which risks to accept and which require additional controls.
Residual risk gives you a measurement framework for those decisions. When you know what exposure remains after current controls, you can compare it against your risk appetite. If residual risk exceeds your tolerance, you need stronger measures. If it falls within acceptable limits, you can allocate resources elsewhere.
Compliance frameworks require this thinking. Standards like ISO 27001, NIST, and SOC 2 explicitly demand that organizations identify and document residual risk. Auditors want to see that you understand what threats persist and have consciously accepted or mitigated them.
Board members and executives need residual risk data to make strategic choices. Should the company enter a new market with higher cyber threats? Should you adopt a new technology with unknown vulnerabilities? These decisions depend on understanding the risk that will remain after standard protections are in place.
Insurance providers increasingly ask about residual risk when pricing cyber policies. They want to know not just what controls you have, but what exposure persists despite those controls.
How to calculate and assess residual risk
Calculating residual risk follows a structured process that moves from identification through quantification to decision making.
- Identify inherent risks across your environment by cataloging threats, vulnerabilities, and potential impacts without considering existing controls.
- Document all current controls, including technical measures, policies, training programs, and response procedures that address each identified risk.
- Assess control effectiveness by testing whether each measure actually reduces the associated threat to the expected degree.
- Calculate residual risk by determining what exposure remains after accounting for functioning controls, typically expressed as likelihood times impact.
- Compare residual risk against your organization’s risk tolerance to identify gaps requiring additional treatment or formal acceptance.
The formula looks simple: Residual Risk = Inherent Risk minus Control Effectiveness. But the challenge lies in accurate measurement.
Many organizations use risk matrices that plot likelihood against impact on a scale from low to high. A threat might start as high inherent risk (likely to occur with severe impact) but drop to medium residual risk after controls reduce either probability or consequences.
Quantitative approaches assign dollar values to potential losses and probability percentages. If a data breach has inherent risk of $2 million loss at 40% annual probability, but controls reduce probability to 10%, your residual risk is $200,000 in expected annual loss.
Qualitative assessments work when precise numbers aren’t available. You might rate risks as critical, high, medium, or low based on expert judgment and comparative analysis.
Common mistakes in residual risk management
Organizations often stumble in predictable ways when handling residual risk. Recognizing these patterns helps you avoid them.
| Mistake | Why It Happens | Better Approach |
|---|---|---|
| Assuming controls eliminate risk | Overconfidence in technical solutions | Test and validate actual effectiveness |
| Ignoring control degradation | Set and forget mentality | Schedule regular control assessments |
| Accepting risk without documentation | Informal decision making | Require written acceptance from accountable parties |
| Using outdated risk assessments | Annual review cycles | Trigger reassessment when environment changes |
| Treating all residual risk equally | Limited prioritization | Rank by business impact and likelihood |
One frequent error is confusing risk transfer with risk elimination. Buying cyber insurance transfers financial consequences but doesn’t reduce the underlying residual risk of a breach occurring. The threat remains. You’ve just shifted who pays for it.
Another trap is failing to reassess residual risk when controls change. You implement a new endpoint detection system and assume residual risk automatically drops. But if the tool isn’t configured properly or staff don’t respond to alerts, actual risk reduction might be minimal.
Organizations also struggle with risk acceptance decisions. Someone needs authority to formally accept residual risk on behalf of the business. Without clear ownership, risks fall through cracks or get accepted by people without appropriate context.
Building an effective residual risk framework
A mature approach to residual risk requires structure, accountability, and continuous improvement.
Start with a risk register that documents every identified threat, associated controls, and calculated residual risk. This living document becomes your single source of truth for risk status across the organization.
Assign risk owners for each category. These individuals, typically senior managers or department heads, hold accountability for ensuring residual risk stays within tolerance. They make acceptance decisions and approve additional controls when needed.
Establish clear risk tolerance levels tied to business objectives. Your organization might accept low residual risk in customer data protection but tolerate higher residual risk in non-critical internal systems. Document these thresholds and the reasoning behind them.
Create a review cadence that matches your environment’s pace of change. Fast-moving technology companies might reassess monthly. Stable industries might review quarterly. Trigger immediate reassessment when major changes occur:
- New systems or technologies deployed
- Significant security incidents
- Regulatory requirement changes
- Business model shifts
- Control failures detected
Integrate residual risk into project planning. Before launching new initiatives, require teams to identify what risks will remain after standard controls are applied. This prevents surprises and ensures conscious decision making.
The most dangerous residual risks are the ones you haven’t identified yet. Build a culture where people actively look for gaps between your controls and actual threats, then speak up when they find them.
Residual risk across different domains
Residual risk manifests differently depending on your industry and threat landscape.
Cybersecurity residual risk typically involves threats that bypass technical controls. Even with perfect patch management, zero-day vulnerabilities create residual risk. Strong authentication reduces unauthorized access but doesn’t eliminate social engineering threats. Encryption protects data at rest but leaves exposure during processing.
Compliance residual risk appears when regulations require controls that can’t guarantee complete protection. GDPR demands data protection measures, but residual risk of breach persists. HIPAA requires safeguards for health information, but human error creates ongoing exposure.
Operational residual risk includes business continuity threats that disaster recovery plans can’t fully eliminate. Your backup systems might fail during the same event that takes down primary systems. Supply chain dependencies create residual risk even with multiple vendors.
Financial residual risk involves market movements, credit defaults, or fraud that controls can reduce but never prevent entirely. Segregation of duties limits fraud opportunity but determined insiders can still collude.
Physical security residual risk remains after access controls, surveillance, and guards are in place. Tailgating, credential theft, or insider threats persist despite preventive measures.
Communicating residual risk to stakeholders
Different audiences need residual risk information presented in ways that match their decision-making needs.
Executives want bottom-line impact. Frame residual risk in business terms: potential revenue loss, reputation damage, regulatory fines, or competitive disadvantage. Use scenarios that connect technical risks to strategic objectives.
Board members need comparison against risk appetite. Show them where residual risks fall relative to established tolerance levels. Highlight any exposures that exceed acceptable thresholds and present options for additional treatment.
Technical teams require detailed breakdowns. Give them specifics about which controls are working, where gaps exist, and what attack vectors remain viable. This enables them to prioritize security improvements effectively.
Compliance officers want documentation that satisfies auditor requirements. Provide evidence that residual risks have been identified, assessed, and either mitigated further or formally accepted by appropriate authorities.
Insurance providers need quantified exposure data. Present residual risk in terms of probable maximum loss, annual loss expectancy, and the specific controls that reduce inherent risk to current levels.
When to accept residual risk versus adding controls
Not every residual risk requires additional treatment. The decision to accept or further mitigate depends on several factors.
Accept residual risk when the cost of additional controls exceeds the expected loss from the risk materializing. If a threat might cause $10,000 in damage once every ten years, spending $50,000 on prevention doesn’t make economic sense.
Accept residual risk when it falls within your documented risk tolerance. If your organization can absorb the potential impact without significant harm to operations, reputation, or financial stability, acceptance is appropriate.
Accept residual risk when no practical controls exist to reduce it further. Some threats, like nation-state attacks on critical infrastructure, can’t be completely prevented with reasonable measures.
Add controls when residual risk exceeds tolerance levels. The gap between current exposure and acceptable exposure justifies investment in stronger measures.
Add controls when regulatory requirements demand specific protection levels regardless of cost-benefit analysis. Compliance often isn’t optional.
Add controls when the risk landscape changes. New attack techniques, emerging vulnerabilities, or increased threat actor interest might push previously acceptable residual risk into unacceptable territory.
Document every acceptance decision. Include who accepted the risk, when, under what circumstances, and when the decision will be reviewed. This creates accountability and prevents forgotten exposures.
Monitoring residual risk over time
Residual risk isn’t static. It changes as your environment, threats, and controls evolve.
Implement continuous monitoring for key risk indicators that signal when residual risk is increasing. These might include failed login attempts, unpatched systems, policy violations, or control failures.
Track control effectiveness metrics. If your email filtering catches 99% of phishing attempts this month but only 85% next month, residual risk from phishing has increased even though nothing else changed.
Watch for environmental shifts that alter the threat landscape. New malware families, publicized vulnerabilities in your technology stack, or geopolitical events can suddenly elevate residual risk.
Conduct periodic penetration testing and red team exercises. These reveal whether residual risk matches your calculations or if gaps exist between assumed and actual control effectiveness.
Review incident data for patterns. If the same type of security event keeps occurring, your residual risk assessment for that threat category might be too optimistic.
Update risk assessments when business changes occur. New products, markets, partnerships, or technologies all introduce fresh inherent risks and alter existing residual risk profiles.
Making residual risk work for your organization
Understanding residual risk transforms it from an abstract concept into a practical management tool. You can’t eliminate every threat, but you can make informed choices about which exposures to accept and which demand action.
Start by documenting what you know. Catalog your current controls and honestly assess what risks remain. Compare those residual risks against your organization’s actual tolerance for loss, disruption, or compliance failure. The gaps between current state and acceptable state become your roadmap for improvement.
Remember that managing residual risk is about enabling business objectives, not preventing all possible harm. Sometimes accepting residual risk is the right choice because it frees resources for higher-priority threats or business opportunities. The key is making that choice consciously, with full awareness of what you’re accepting and clear ownership of the decision.
Build residual risk assessment into your regular rhythm. Make it part of project planning, quarterly reviews, and strategic discussions. When everyone in your organization understands not just what controls exist but what threats persist despite those controls, you create a culture that’s genuinely prepared rather than just compliant.
